I’ll give you some more things to consider.
How to add support for some post-quantum signature scheme?
That’s relatively easy, it’s a drop-in, we can extend OP_CHECKSIG[VERIFY], OP_CHECKMULTISIG[VERIFY], and OP_CHECKSIG[VERIFY] just like we did when we added support for Schnorr signatures and Schnorr multisig: the opcode reads the length of pushed signature and from that determines how to interpret it and which method to use to validate.
With post-quantum crypto, keys & signatures would be bigger so same method is usable there: opcode can internally switch what scheme it uses based on the length of arguments.
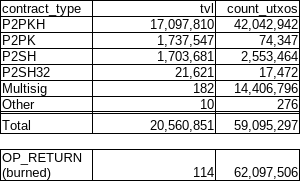
Addresses would stay the same, UTXO size would stay the same, however input sizes would grow since they’d have to reveal bigger pubkeys and signatures, lowering the network’s TPS per megabyte of block size. See here for more info.
How to migrate from safe-at-rest elliptic curve P2PKH to post-quantum P2PKH
If quantum computers would become fast enough, adversary could intercept your transaction, discover your public key, and attempt to generate an alternative signature and replace your TX with his.
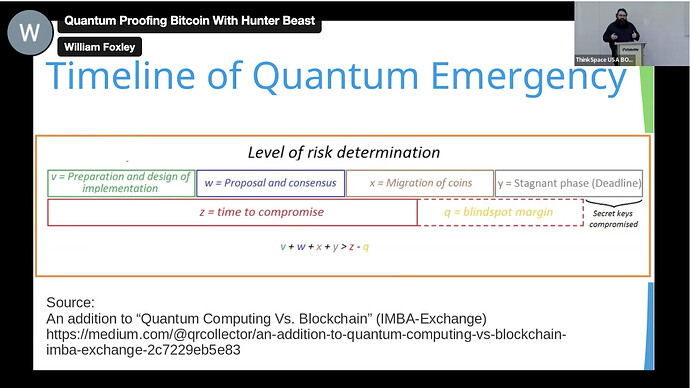
If that was a real threat, a new consensus rule could require and intermediate step for transferring funds from such UTXOs, a commit-delay-reveal scheme:
While your pubkey is still secret, you’d create a TX, hash it, then publish the hash on the chain. After the hash has been embedded to a safe depth, you’d publish the TX and reference the hash.
The adversary could generate an alternative TX, but he could not have an aged hash ready, and by the time he makes one, your TX will have been mined.
The paper linked above describes the method for migration in detail:
Can I store BCH in a quantum-safe address today?
Nice thing about Bitcoin Cash having powerful scripting capabilities is that it’s already possible to lock up funds in a quantum-safe contract (P2SH32), one that requires an aged pre-commitment + signature.
I outlined it in the P2SH bulletin at the end of section 5.
Are 160-bit P2PKH addresses that DID NOT reveal their pubkey vulnerable?
Theoretically yes, practically no. Grover’s algorithm could find an alternative spending key in a finite amount of time BUT:
Assuming a clock speed on scale of GHz, this would take about 10 million years. Important to note is that splitting the work and doing it in parallel is not as beneficial as with classic computers because it would offer only a quadratic speedup (Fluhrer, S., Reassessing Grover’s Algorithm). In other words, doing the work in 1 year would require building 100 trillion quantum computers because
sqrt(100T) == 10M. Therefore, we can say that breaking a 160-bit hash preimage is physically possible because 10M years is a finite amount of time and less than age of the universe. However, it is still infeasible.
What about abandoned coins with pubkeys revealed?
They’d be free for the taking because original owners wouldn’t act during the window of opportunity to move the coins to quantum-resistant storage and so they’re as good as gone as soon as Shor’s algorithm becomes feasible. I guess it can be considered a bounty for the first to implement Shor’s