CashFusion’s transaction privacy protocol is one of BCH’s crown jewels. What if it could be made even more robust through a Red Team analysis? Red Team analysis is a concept from the fields of cybersecurity and military planning that involves investigating the strength of security measures by simulating attacks on the defenses and then developing improvements to those security measures.
My question to you all is whether there is interest in performing this kind of analysis on CashFusion. It’s almost a certainty that CipherTrace, Chainalysis, and their ilk are Red Teaming CashFusion for real right now – and they’re playing for keeps. We need to know what the weaknesses are, if any, and address them.
Putting fresh eyes onto privacy protocols has been fruitful for other coins. Last year, a serious flaw in Wasabi Wallet’s BTC CoinJoin protocol was discovered by external researchers. Just a few weeks ago an external engineer discovered a significant privacy bug in Monero’s reference wallet.
Didn’t the June 2020 audit by Kudelski Security already do this?
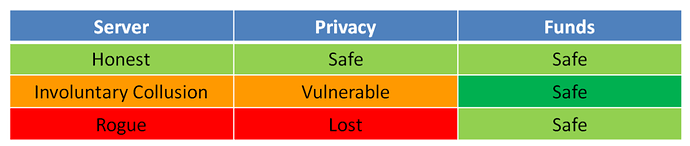
No, not really. The audit primarily dealt with ensuring that the protocol could not steal coins from CashFusion participants and ensuring secure communication channels while the CashFusion transactions were being negotiated by the central CashFusion server and participants. They did analyze the privacy guarantees, but not very thoroughly.
One of the audit’s recommendations was:
Furthermore, a higher level of assurance could be achieved by providing a thorough security analysis of the protocol under realistic adversarial conditions. Specifically, we would recommend to add: A threat model…[and] more rigorous analysis of the amount linkage risks (the combinatorial arguments is a good start.)…The exercise of working out such documents may in turn reveal overlooked design aspects or unforeseen optimizations.
The audit goes on to state:
The authors of CashFusion argue that, for a reasonable amount of players and components, the sheer number of combinations makes finding these combinations impossible. However, we notice that this is only true for a pure brute-forcing approach. The problem in question reminds vaguely of the problem of bin packing where heuristic algorithms much more efficient than brute-forcing are known. It is not obvious how a direct reduction between the two problems can be found, but we recommend nevertheless checking carefully this security argument against state-of-the-art works found in combinatorics literature.
I have confirmed with Electron Cash lead maintainer Jonald Fyookball that they have not yet made progress on this recommendation from the audit. If I were to do a Red Team analysis, I would follow responsible disclosure procedures by informing Electron Cash developers of all significant findings before they are revealed publicly, if at all.
Who am I?
Long-turn lurker, recently a participant. I’m an empirical microeconomist. That means that I use real-world data, rather than mathematical theory, to investigate economic questions at the level of consumers, businesses, and industries. While reading about bitcoin’s skyrocketing price in 2017, I set out to see if I could prove to myself the hypothesis that bitcoin was just a classic tulip-mania-style asset bubble. I tried to keep an open mind, and the more I read the more I recognized that bitcoin does actually present a solution to many real economic problems. So I rejected my initial hypothesis and have since kept abreast of developments in cryptocurrency.
To demonstrate that I’ve been around for years I am able to cryptographically sign a statement with the private key of a 2017-vintage BCH address and submit it to a trusted community member for verification. (Not publicly though since that address has been KYC’ed to hell and back.)
As a start, I’ve built a simple public-facing web app at https://fusionstats.redteam.cash/ that displays basic stats about all CashFusions to date. The intention was to mimic stats dot cash (which seems to be in maintenance mode at the moment) but with some additional interactivity.
(Post has been cross-posted to reddit: https://www.reddit.com/r/btc/comments/oymjz2/is_there_interest_in_a_red_team_analysis_of/ )