This outlines contract design, and it is possible to implement them now. Having header introspection opcode would help make it more robust and simpler. Consensus upgrade would only have to overload P2PK and P2PKH spends and force them to migrate to the challenge contract.
Open question: how to deal with multisig. It would require a more complex challenge contract and interactive spend.
Quantum-Resistant Bitcoin Cash: A Challenge-Based Transition Protocol
Abstract
We propose a protocol enabling secure transition of Bitcoin Cash funds from quantum-vulnerable addresses to quantum-resistant ones, functional even after ECDSA is compromised. The protocol uses aged commitments as proof of ownership, with a challenge mechanism allowing older commitments to displace newer ones. Unlike previous proposals, this design creates uncertainty for attackers: they cannot know whether a prior commitment exists, providing deterrence even for already-exposed public keys.
1. Background
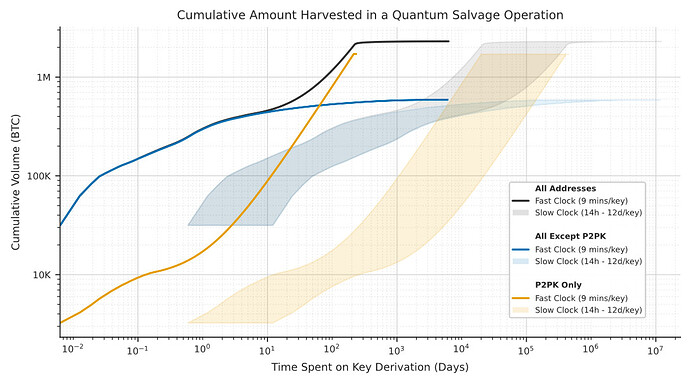
Bitcoin Cash currently uses ECDSA signatures over the secp256k1 curve. Shor’s algorithm, running on a sufficiently powerful quantum computer, can derive private keys from public keys in polynomial time. This threatens:
- P2PK outputs: public key always exposed
- Spent-from P2PKH: public key revealed at first spend
- Reused P2PKH: public key exposed on other chains or through address reuse
Previous work by Stewart et al. (2018) proposed a commit-delay-reveal protocol allowing users to transition funds securely. However, their design executes immediately upon reveal: if an attacker reveals first, funds are lost. We extend this with a challenge period during which older commitments can displace newer ones.
2. Threat Model
We consider a quantum-capable adversary (QCA) who can:
- Derive any ECDSA private key from its public key
- Monitor the network and blockchain
- Create valid signatures for any exposed public key
We assume the QCA cannot:
- Break cryptographic hash functions (SHA-256, RIPEMD-160)
- Rewrite deep blockchain history beyond practical reorganization limits
- Predict secrets chosen by honest users
3. Protocol Overview
The protocol has four phases: commit, reveal, challenge, and finalize.
3.1 Commit
A user with public key pk creates a commitment:
C = H(pk \,\|\, secret \,\|\, qr\_address)
where secret is a random value known only to him and qr\_address is a quantum-resistant destination address (for example, a Quantumroot vault address). The commitment is published on-chain by sending dust to a P2SH address derived from C. The user retains secret and qr\_address privately.
The commitment is unlinkable: observers cannot determine which public key it protects.
For users of HD wallets, the secret can be derived deterministically from the seed, for example as H(xpriv \,\|\, privkey \,\|\, \texttt{'qr'}), eliminating the need for separate secret backup.
3.2 Reveal
After the commitment has aged sufficiently, the user reveals it by spending the commitment UTXO. The reveal transaction:
- Exposes pk, secret, and qr\_address
- Proves knowledge of the ECDSA private key via a valid signature
- Creates an NFT credential recording the commitment’s proven age
The signature requirement ensures that pre-quantum, only the legitimate owner can reveal. Post-quantum, anyone can sign, but the commitment’s age, established pre-quantum, determines priority.
The NFT credential encodes:
| Field | Description |
|---|---|
| pk_hash | Hash of the public key this credential protects |
| qr_address | Quantum-resistant destination for funds |
| accumulated_age | Proven age in blocks |
3.3 Age Accumulation
Relative timelocks (nSequence) are limited to approximately 65,535 blocks, or roughly 1.25 years. The reveal transaction sets nSequence to the maximum valid value; consensus rules enforce that this cannot exceed the actual UTXO age. The NFT records this value as its initial accumulated age.
Commitments older than this limit can accumulate additional age through successive transactions. Each aging transaction spends the NFT with maximum nSequence and recreates it with the accumulated_age field incremented accordingly. This allows arbitrarily old commitments to prove their full age.
3.4 Challenge
When spending a quantum-vulnerable UTXO (P2PK or P2PKH) after protocol activation, the spend must reference a valid NFT credential and route through a challenge contract. The challenge contract:
- Records the initiating credential’s accumulated age as the incumbent
- Opens a challenge window
- Accepts challenges from credentials with strictly greater age for the same public key
- Updates the incumbent only when a challenger proves an older commitment
A challenger must present an NFT credential for the same public key with accumulated_age strictly exceeding the incumbent. Ties favor the incumbent: strictly greater age is required to displace. This prevents spam, as registering a losing claim accomplishes nothing.
3.5 Finalize
After the challenge window expires, funds transfer to the qr\_address specified by the surviving credential. The NFT credential is not consumed and may be reused for other UTXOs locked to the same public key.
4. Security Properties
4.1 Pre-Quantum Security
Only the legitimate owner can reveal a commitment, as revelation requires a valid ECDSA signature. Attackers cannot create useful commitments for keys they do not control.
4.2 Post-Quantum Security
Once quantum computers exist, attackers can sign for any exposed public key. However:
- For unexposed P2PKH, the attacker does not know which public key to target until spend time, too late to create an aged commitment
- For exposed keys, security depends on the legitimate owner having committed earlier
The challenge mechanism ensures the oldest commitment wins, regardless of who reaches the reveal or challenge phase first.
4.3 Deterrence Through Uncertainty
Even for long-exposed P2PK outputs, including Satoshi-era coins, attackers face uncertainty. They cannot know whether:
- The original owner holds an aged commitment
- Another party (heir, custodian, or earlier attacker) holds an aged commitment
- No commitment exists
This uncertainty reduces the expected value of attacks, as initiating a challenge risks losing to an older commitment. An attacker who spends resources to derive a private key and initiate a challenge may find his efforts wasted when an older commitment surfaces.
5. Post-Quantum Plausible Deniability and Provenance
After quantum computers become available, ECDSA signatures no longer prove identity. Both original owners and quantum-capable parties can produce valid signatures, creating bilateral plausible deniability:
- An original owner moving his funds can claim to be a quantum salvager
- A quantum salvager can claim to be the original owner
This ambiguity is inherent to the post-quantum environment and cannot be resolved cryptographically. However, the commitment mechanism provides meaningful signals about provenance.
5.1 Cost Asymmetry
Only the original owner can create a commitment at near-zero cost (just dust for the commitment UTXO). This advantage persists both before and after quantum computers arrive. A quantum-capable party must:
- Derive the private key using expensive quantum computation
- Create a commitment that will necessarily be younger than any existing commitment from the original owner
- Risk losing the challenge to a prior commitment
Even an original owner who sleeps through Q-day retains an edge: if no attacker has yet targeted his address, he can wake up, create a commitment, and begin aging it. He pays only dust, while any attacker targeting him later must perform quantum key derivation and will produce a younger commitment that loses the challenge.
This asymmetry means that coins moved with well-aged commitments are more likely to be controlled by original owners, providing a useful signal for counterparties assessing provenance risk.
5.2 Salvage Framework
For coins moved with young commitments after Q-day, particularly from long-dormant addresses, existing salvage principles from property law may apply. The quantum-capable party took a risk by initiating a challenge: if no older commitment surfaced during the challenge window, the original owner effectively abandoned his claim. The salvager invested resources (quantum computation, commitment creation, waiting period) and bore the risk of losing to a prior commitment.
This framing aligns with established legal concepts of abandoned property and salvage rights, potentially providing a path for these coins to enter circulation without tainting the broader supply. Recipients can assess risk based on commitment age: coins with pre-quantum commitments carry strong provenance, while coins with post-quantum commitments carry weaker but legally defensible provenance under salvage principles.
5.3 Implications for Fungibility
The protocol thus creates a spectrum of provenance strength rather than a binary distinction:
| Commitment Age | Provenance Signal |
|---|---|
| Years pre-quantum | Very likely original owner |
| Months pre-quantum | Likely original owner |
| Post-quantum, unchallenged | Possible salvage, legal provenance |
| Post-quantum, challenged and won | Demonstrated superior claim |
This graduated approach allows the market to price provenance risk appropriately while avoiding categorical exclusion of post-quantum-moved coins from circulation.
6. Challenge Window Parameters
The challenge window duration may vary based on UTXO characteristics:
| UTXO Type | Suggested Window | Rationale |
|---|---|---|
| Ancient P2PK (2009-2012) | 12 months | Owners may be deceased or slow to respond |
| Dormant P2PKH (years inactive) | 6 months | Potentially recoverable, needs time |
| Recently active | 1-3 months | Owner clearly active, will notice quickly |
These parameters can be encoded in the challenge contract and balance security (time for legitimate owners to respond) against usability (funds locked during challenge).
7. Consensus Activation
The protocol requires a new consensus rule: P2PK and P2PKH spends must route through the challenge contract with a valid NFT credential.
Pre-activation (announcement to activation, suggested 12+ months):
- Users create and age commitments
- No spend restrictions yet
- Wallets encourage commitment creation
Post-activation:
- Uncommitted UTXOs cannot be spent, as no valid credential exists to initiate a challenge
- Committed UTXOs spend through the challenge mechanism
- Attackers cannot steal uncommitted funds; such funds remain frozen
This approach is gentler than immediate theft risk. Users who fail to commit before activation lose liquidity but not funds: they can still create commitments, wait for aging, and eventually spend.
8. Efficiency
A single commitment and reveal covers all UTXOs sharing a public key. Users with many UTXOs need only:
- One commitment transaction (dust cost)
- One reveal transaction (creates reusable NFT credential)
- One challenge period per UTXO spent
The NFT credential persists across spends, amortizing setup cost over all UTXOs controlled by the same key.
9. Integration with Quantum-Resistant Wallets
The qr\_address in a commitment can point to any quantum-resistant contract. Quantumroot vaults, as described by Dreyzehner (2025), provide an efficient destination offering 256-bit classical and 128-bit quantum security using only SHA-256. Quantumroot supports efficient batch operations: sweeps of 400+ unique addresses or 800+ inputs fit in a single 100KB transaction, making it well suited for migration scenarios where many UTXOs must be moved during a quantum emergency.
10. Limitations
Advance planning required: Users must commit before quantum computers arrive. Uncommitted funds become frozen at activation.
Challenge period delays: Every spend incurs a challenge window delay, eliminating instant transactions for quantum-vulnerable address types.
Age accumulation overhead: Very old commitments (multiple years) require multiple transactions to prove full age due to the nSequence limitation.
11. Potential Consensus Upgrades
Several future consensus changes could improve the protocol:
Mature header introspection opcode: A new opcode allowing contracts to verify SPV proofs against block headers would enable direct verification of commitment age without relying on nSequence. This would eliminate the age accumulation overhead for old commitments.
Extended nSequence field: Expanding the transaction format to allow wider nSequence values would remove the ~65,535 block limitation, allowing even very old commitments to prove their full age in a single reveal transaction.
12. Conclusion
We present a challenge-based protocol for transitioning Bitcoin Cash to quantum resistance. By separating commitment from revelation, requiring signatures for revelation, and allowing older commitments to displace newer ones during a challenge period, the protocol provides security even when ECDSA is fully compromised. The uncertainty created by unlinkable commitments provides deterrence even for already-exposed public keys, extending partial protection to legacy outputs including those from Bitcoin’s earliest blocks. The persistent cost asymmetry between original owners and quantum-capable parties, combined with the challenge mechanism, creates a framework where post-quantum coin movements can be understood through established salvage principles, supporting continued fungibility of the money supply.
References
Stewart, I., Ilie, D., Zamyatin, A., Werner, S., Torshizi, M.F., & Knottenbelt, W.J. (2018). Committing to quantum resistance: A slow defence for Bitcoin against a fast quantum computing attack. IACR Cryptology ePrint Archive, 2018/213. Committing to Quantum Resistance: A Slow Defence for Bitcoin against a Fast Quantum Computing Attack
bitcoincashautist (2023). Quantum-resistant one-time-use lock. Bitcoin Cash Research Forum. Quantum-resistant One-time-use Lock
Dreyzehner, J. (2025). Quantumroot: Quantum-Secure Vaults for Bitcoin Cash. Quantumroot: Quantum-Secure Vaults for Bitcoin Cash